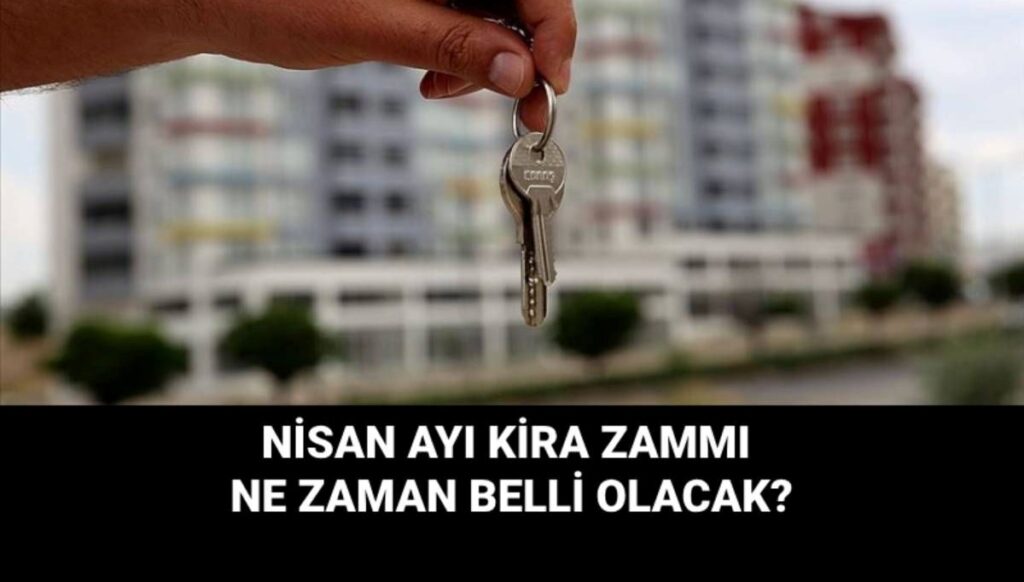
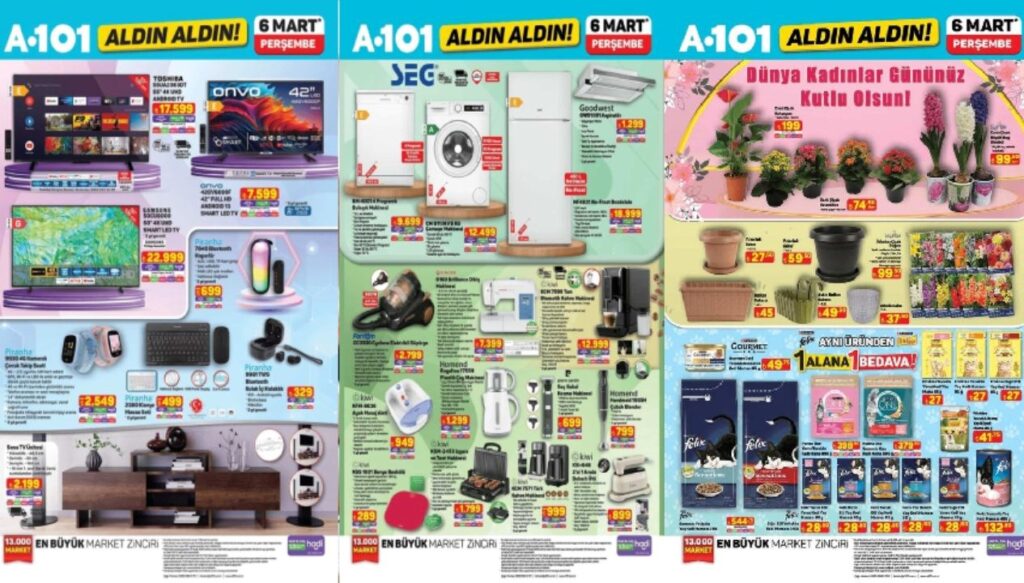
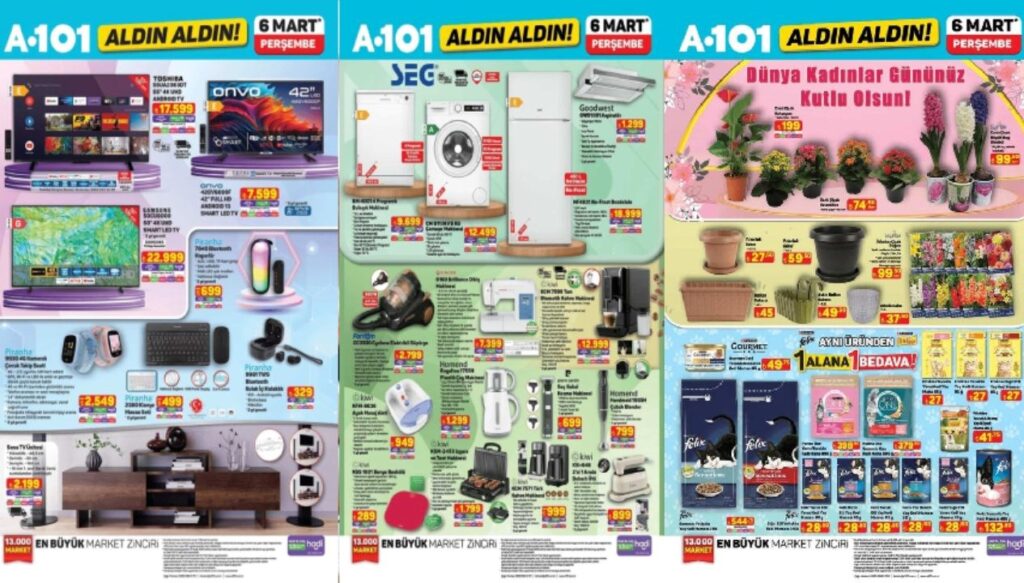
Stolen Funds Laundered: Bybit Hackers Move 62,200 ETH More

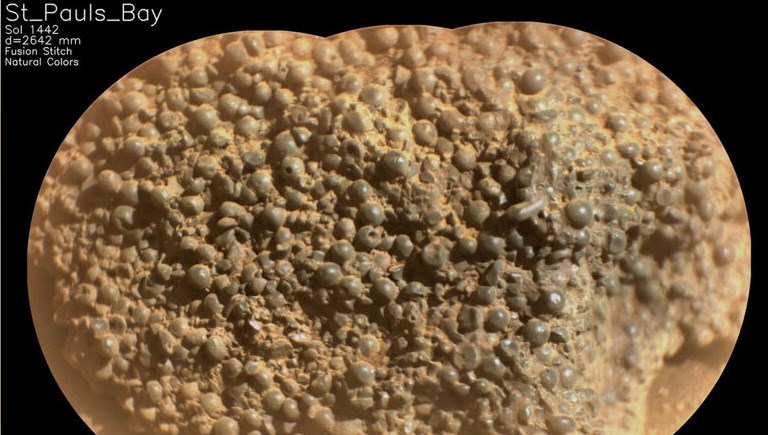
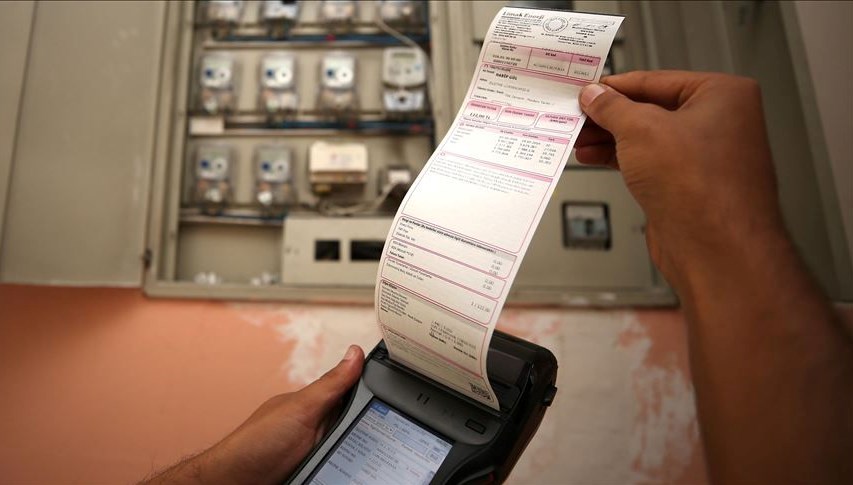
Following the $1.4 billion Bybit hack, the Lazarus Group with North Korean ties continues to launder stolen funds. On March 1st, hackers transferred an additional 62,200 ETH (approximately $138 million), bringing the total ETH disposed of to 343,000. Blockchain analysis firms predict that if the current pace is maintained, the remaining 156,500 ETH could be entirely laundered in the next three days. While the FBI officially confirmed the North Korean connection to the attack, authorities indicate hackers converted the stolen funds into Bitcoin and other crypto assets.
The Lazarus Group, linked to North Korea, persists in laundering stolen funds following the $1.4 billion Bybit hack. The hackers moved 62,200 ETH (about $138 million) on March 1st, totaling 343,000 ETH so far. With this latest move, the remaining Ethereum from the February 21st breach decreased to 156,500 ETH. The blockchain analysis firm EmberCN predicts that if hackers maintain their current transfer rate, the remaining funds could be entirely laundered within the next three days. Despite the FBI’s official involvement and blacklisting of addresses tied to the stolen funds, cybercriminals are swiftly pushing forward.
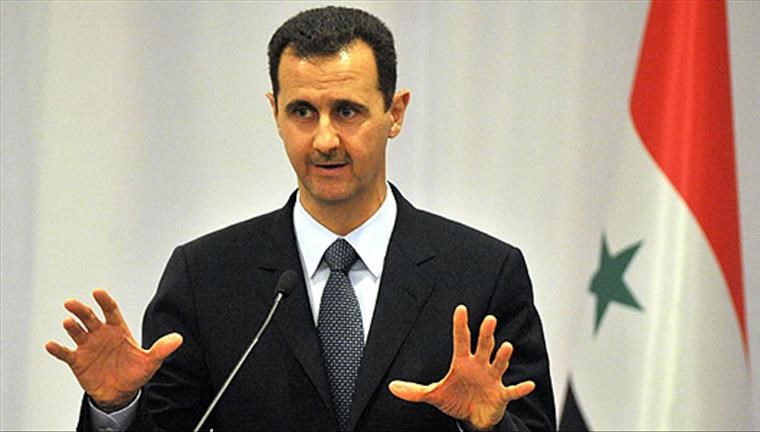
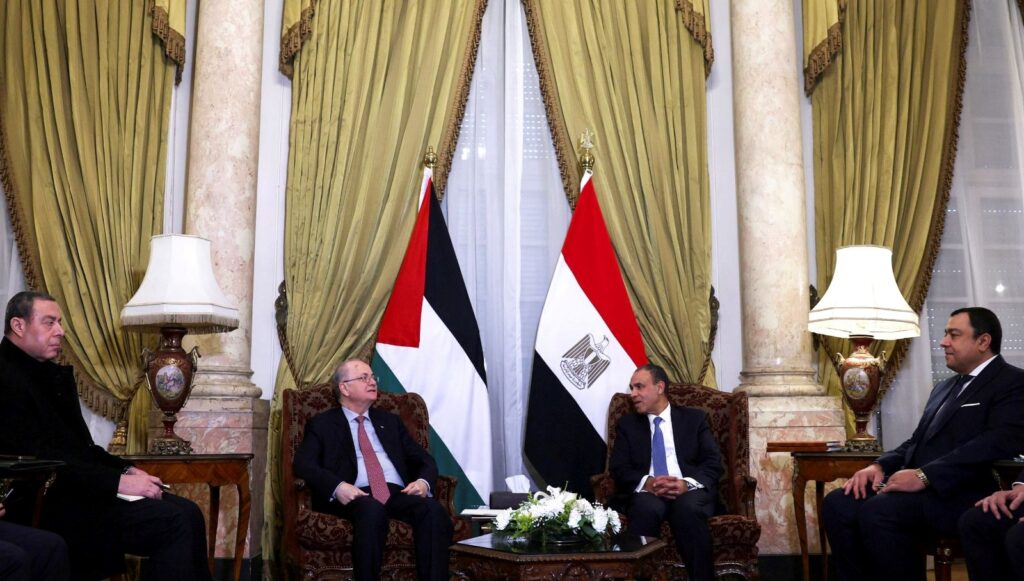
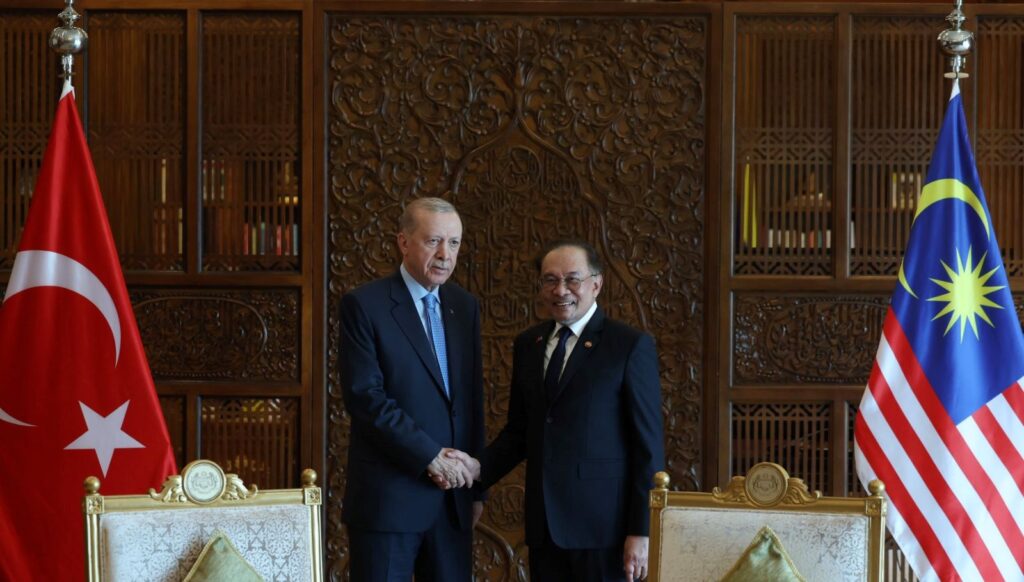
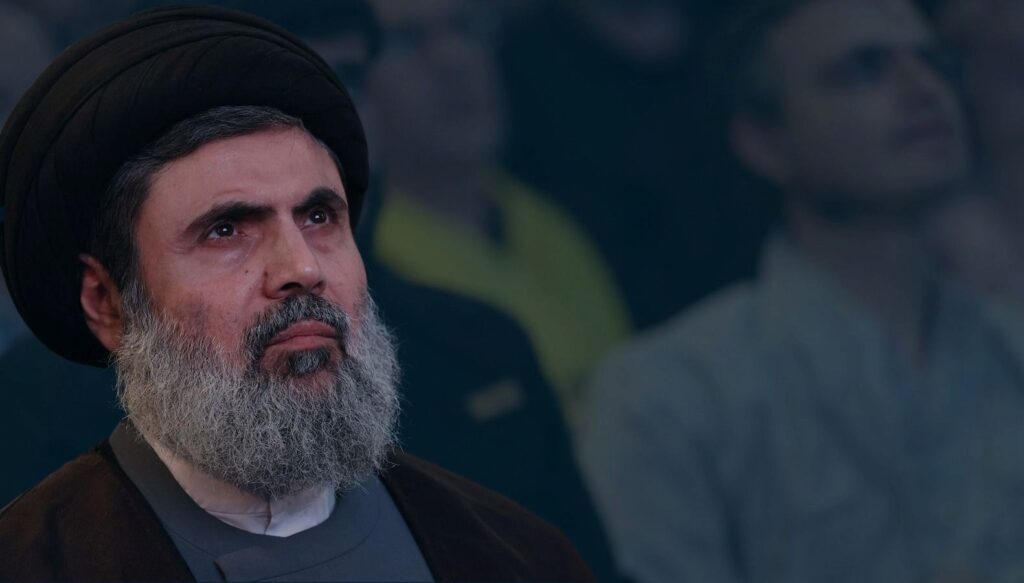
FBI Confirms North Korean Connection
In a public announcement on February 26th, the FBI officially confirmed the Bybit attack as a North Korean-linked operation. Officials mentioned that North Korea has long engaged in crypto asset theft to attempt illegal fund laundering. U.S. authorities define this specific North Korean cyber operation as “TraderTraitor.” According to the FBI, the TraderTraitor attackers are rapidly distributing stolen funds to thousands of addresses across various blockchains in an attempt to launder them. The conversion of ETH to Bitcoin and other digital assets by hackers was also verified.
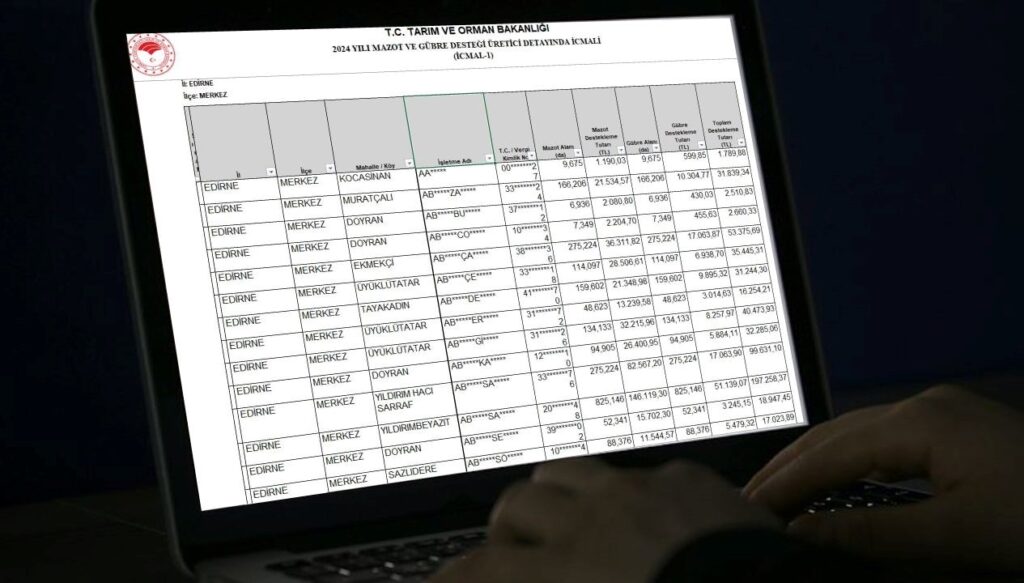
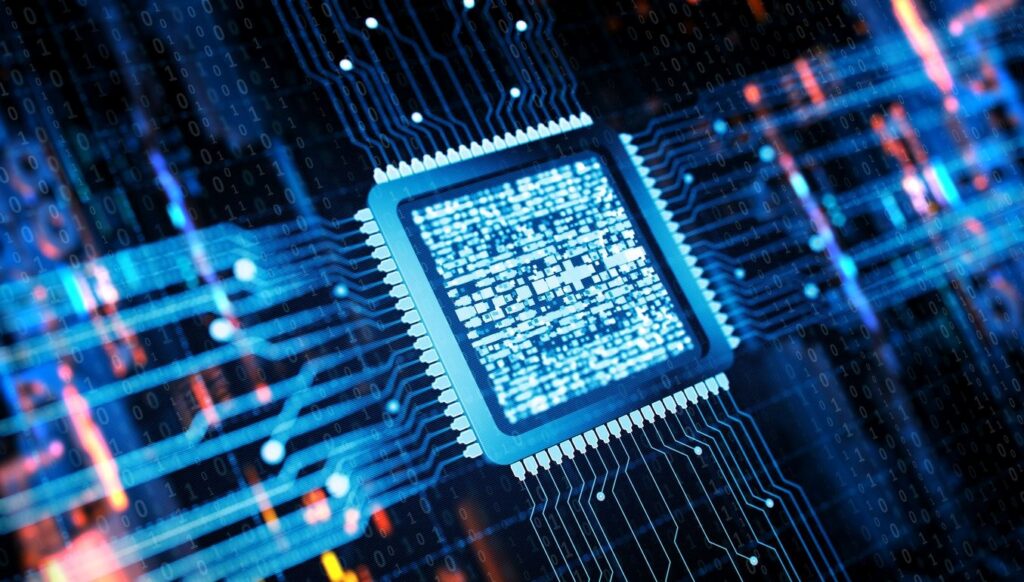
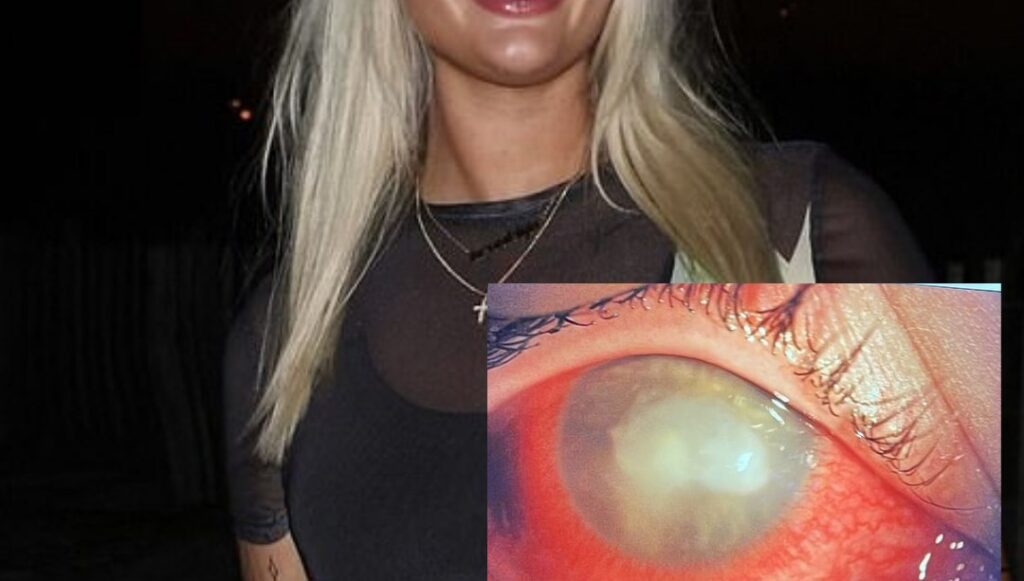
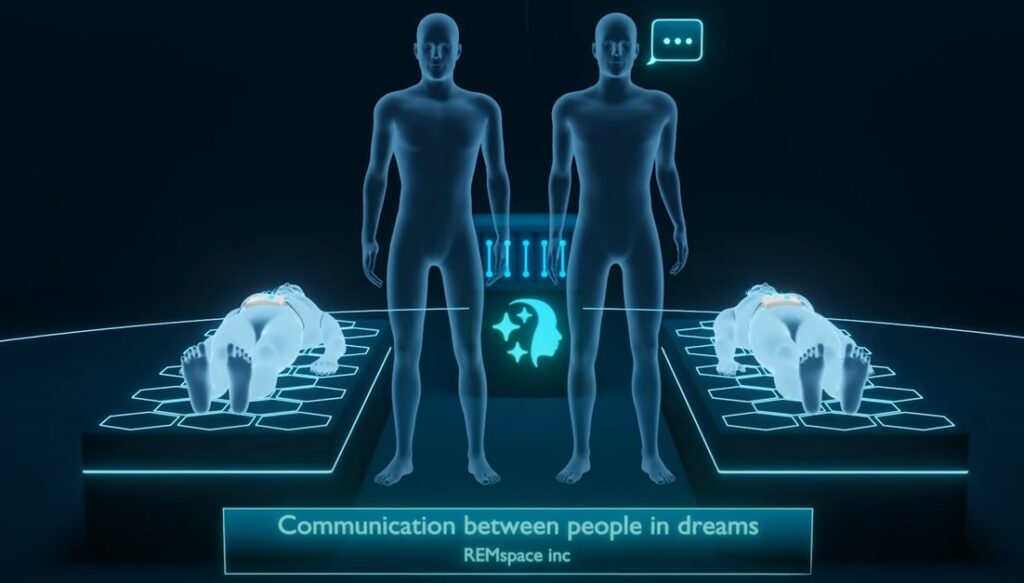
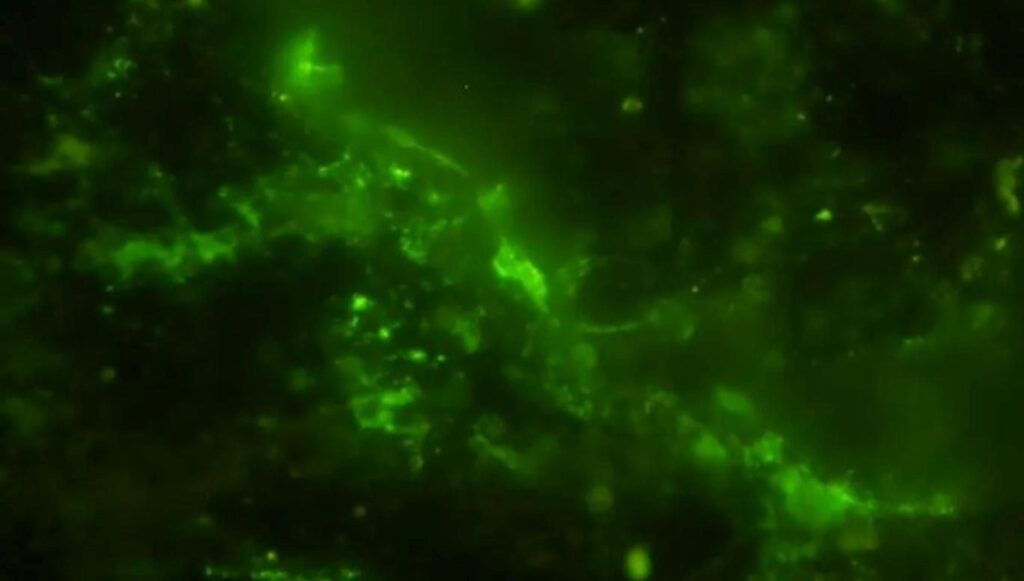
As the FBI shares addresses associated with hackers, blockchain analysis firm Elliptic marked more than 11,000 wallet addresses linked to the attack. Cybercriminals are utilizing decentralized exchanges (DEX), cross-chain bridges, and instant swap services to conceal the trail of stolen funds. Moreover, they are leveraging mixing techniques common in large-scale crypto money laundering operations.
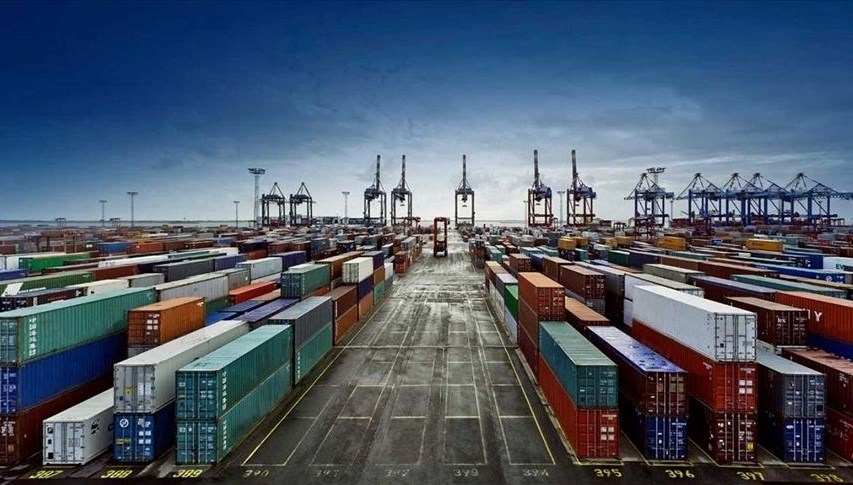
Attack Scale and Fund Fate
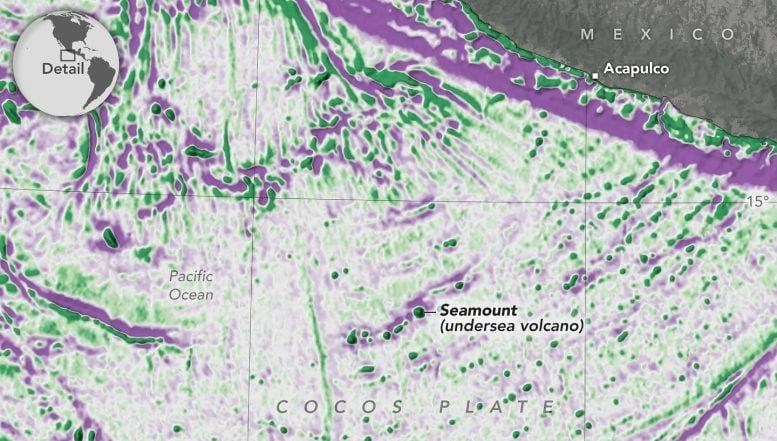
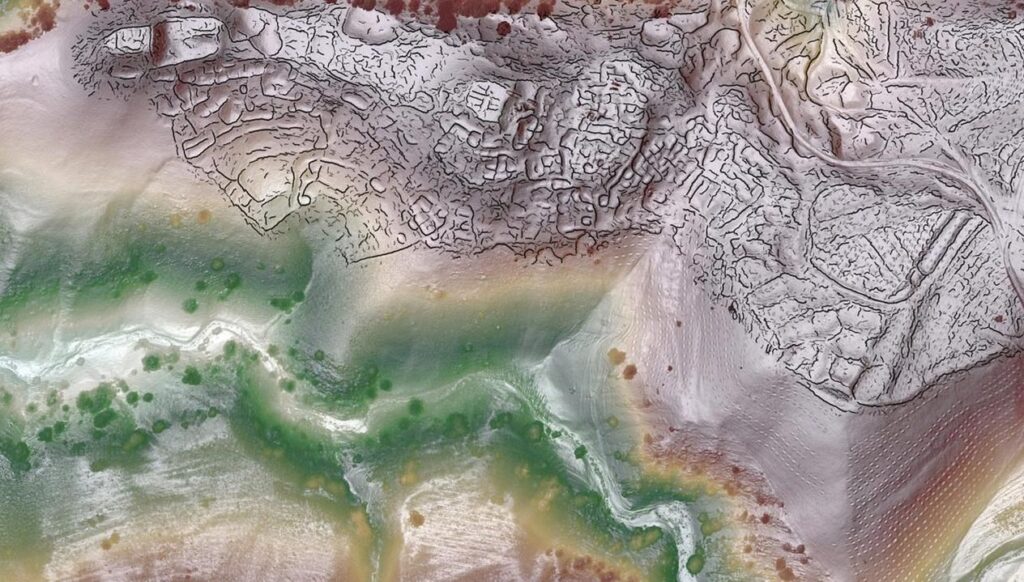
The Bybit hack on February 21, 2025, resulted in the theft of a total of 499,000 ETH. Currently, 343,000 ETH, equivalent to 68.7% of these funds, have been laundered by moving them to different wallets. The FBI assesses that hackers will attempt to convert the remaining assets into fiat currency. Officials call for active support from the private sector and the crypto ecosystem. Operators of RPC nodes, crypto exchanges, DeFi platforms, blockchain analytics firms, and various organizations are requested to block transactions connected to addresses used by hackers.
Chainalysis, a blockchain analysis company, notes that hackers are using different techniques to conceal their traces. They are converting ETH into Bitcoin, DAI stablecoin, and other assets. One striking point is the hackers’ continued transfer of funds through decentralized exchanges without Know Your Customer (KYC) procedures.
Growing Concerns in the Industry
The Bybit attack once again highlights the significant damages cyber vulnerabilities in the cryptocurrency ecosystem can cause. The swift laundering of stolen assets by North Korean hacker groups, especially using DeFi services, raises the need for regulation in the decentralized finance ecosystem. While the FBI and other international law enforcement agencies intensively work to stop hacker activities, the measures taken by the crypto community will determine the course of this process. However, considering the success achieved by the Lazarus Group so far, the possibility of a significant portion of stolen funds being converted into fiat currency in the coming days appears highly likely.